Full Control Over Your Security Data Pipeline.
Security pipelines break quietly. Dropped packets, misconfigured sources, and silent failures go unnoticed until logs stop arriving at your SIEM. By then, the damage is done.
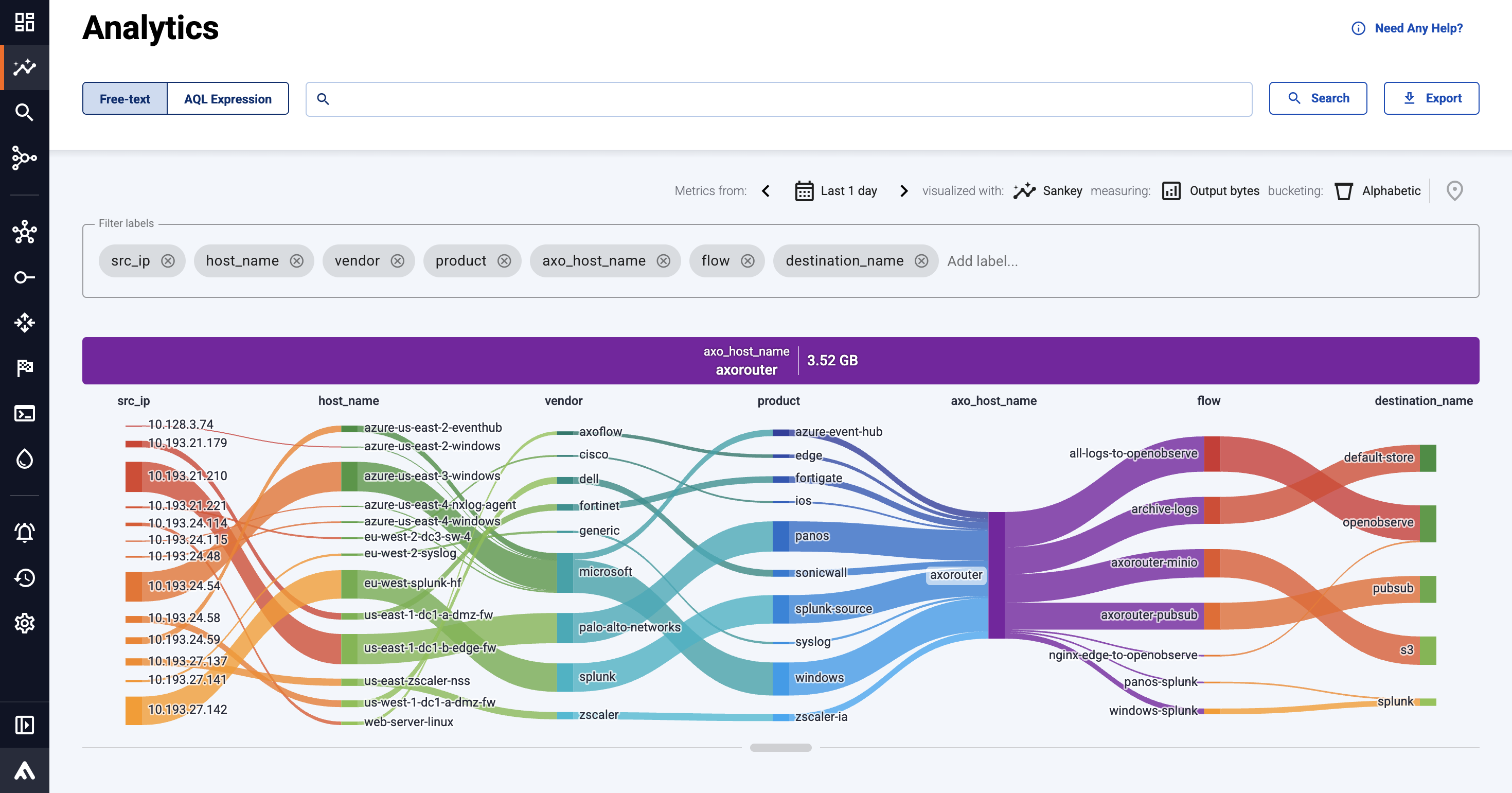
See everything. Know instantly.
Real-time flow analytics and a dynamic topology view give you a live map of your entire pipeline — throughput, health, and data issues visible at a glance, from edge to SIEM.
Catch problems before they catch you.
Proactive alerts for dropped packets, unavailable hosts, disk pressure, and unusual traffic patterns notify you and trigger IT workflows before failures reach your SOC.
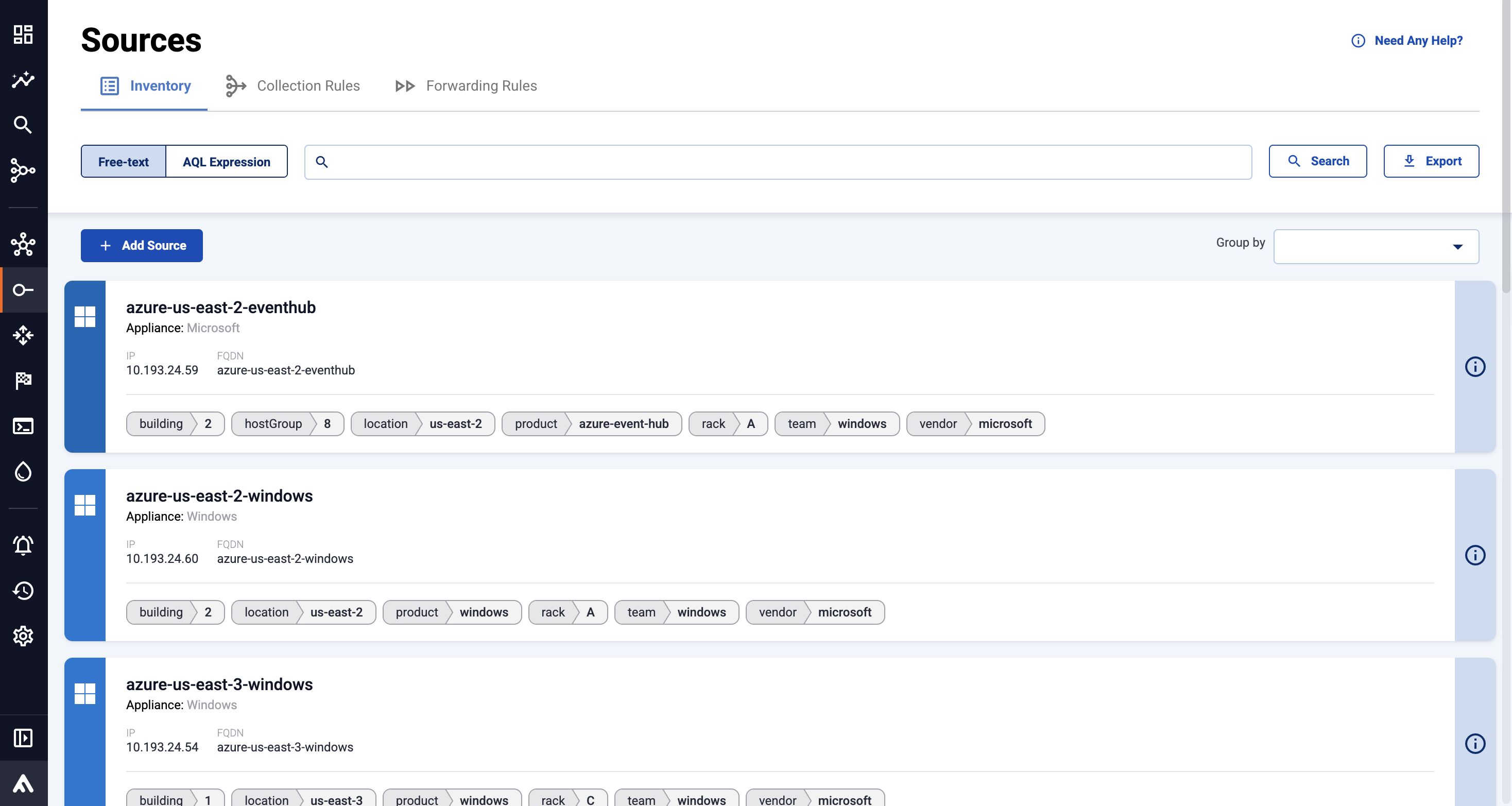
Manage everything from one place.
Configure, monitor, and troubleshoot your entire pipeline from a single web-based interface. No CLI expertise needed — any team member can operate it from day one.
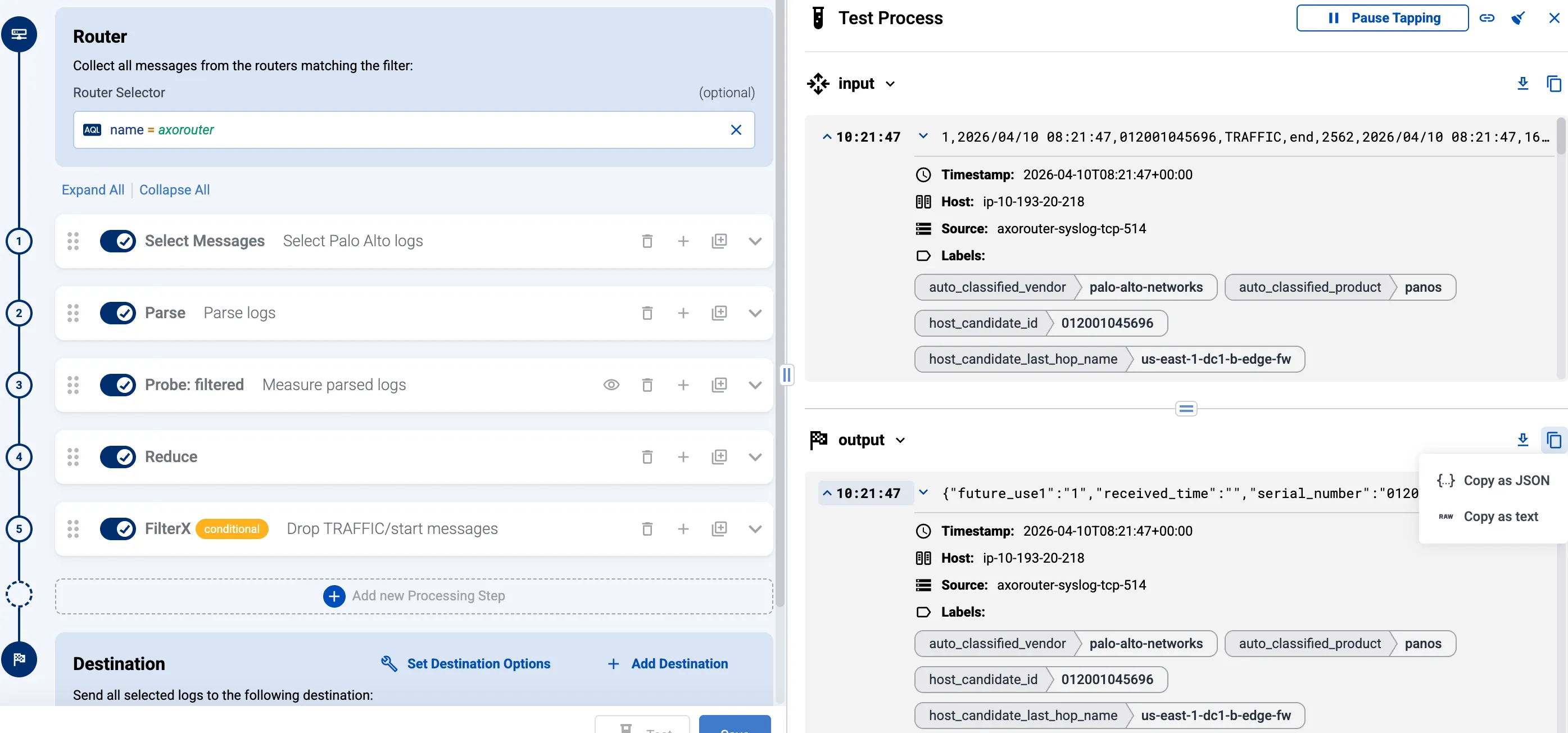
Automatic classification
Avoid custom coding and maintainance hassle. Our classification engine fingerprints incoming data matching it with Axoflow's continuously updated database so you know what data is flowing.
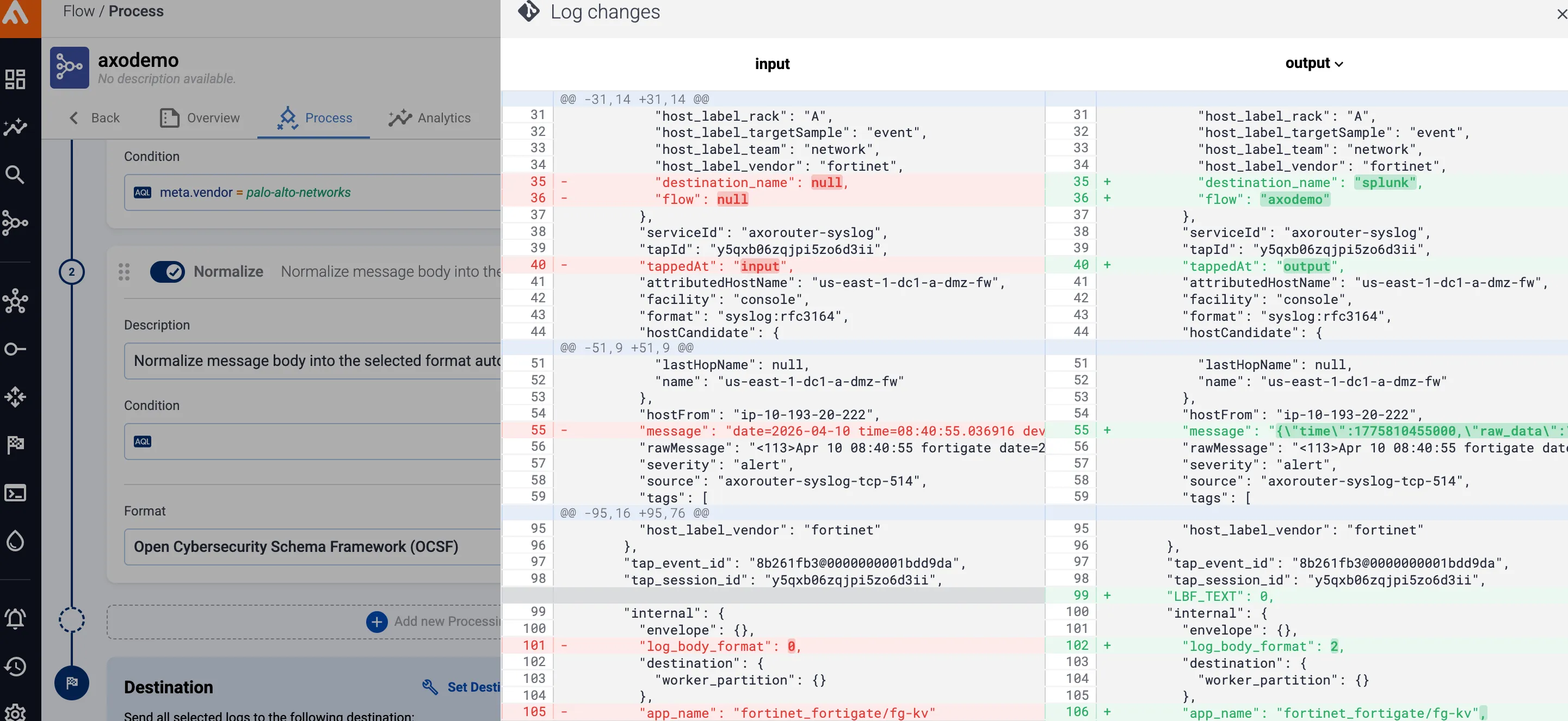
Normalization
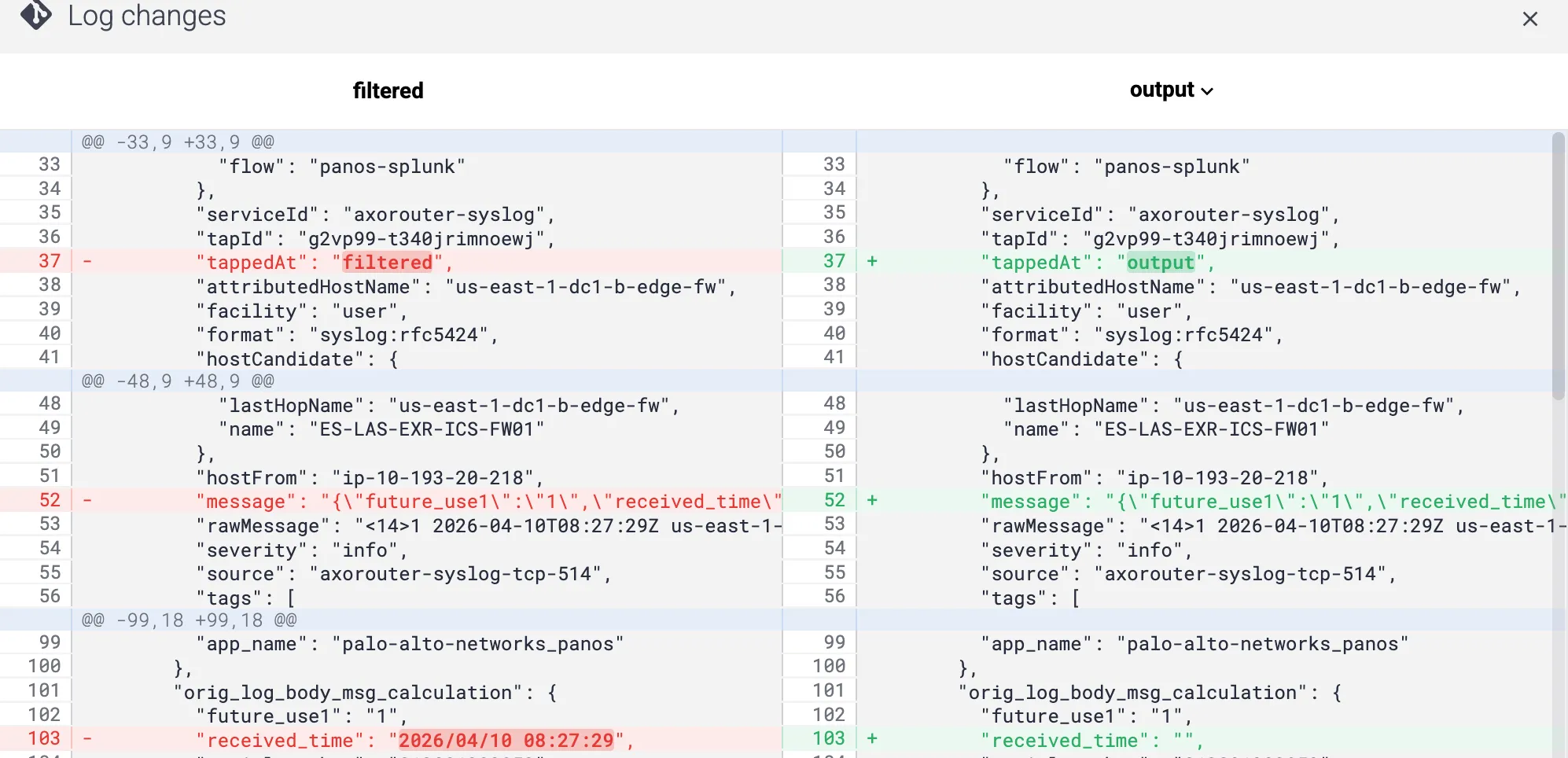
Deliver analyst-ready, destination-friendly data automatically. Consistent schemas, timestamps, and attributes mean detection engineers and SIEM queries work immediately with zero manual reformatting effort.
Parsing
Turn raw logs into structured, actionable intelligence automatically. With hundreds of supported sources parsed out of the box, analysts spend less time on data prep and more time investigating threats.
Enrichment
Give analysts richer context immediately. Automatic enrichment with geolocation, timestamps, host, and vendor data accelerates triage and improves detection accuracy without additional manual investigation steps.